Swiss Domain Security Report Q4 2023

Hi All,
I’ve published a new Swiss Domain Security Report Q4 2023 to rise awareness about the available Security technologies around Domains and Mailsecurity. It shows the adoption of diffrent technologies for the whole .ch TLD (Top Level Domain).
Hope you enjoy it and learn something. Let’s improve the Security in Switzerland!
Note: I am a private Person and this is just a Hobby Project. But i still believe this Report can be useful as an Overview of the Mail- and Domain Security in Switzerland.
Journey
2015
In 2015 i wanted to know how many SMTP Servers used STARTTLS, SPF, DKIM, DMARC. I’ve programmed a Webspider with PowerShell and collected about 100'000 Domains. Then made another Script that queried those domains and made SMTP Connect to find out if STARTTLS was in the ELHO Response. The Result was a Report of about 100'000 Domains from the .ch Top Level Domain.
The Results from 2015 (from a sample of 100'000 .ch Domains):
- About 90% of the Domains used MX
- About 75% of the SMTP Servers offered STARTTLS
- About 28% of the Domains with MX had an SPF Record
- About 1% or less DKIM and DMARC was barely present
2022
In 2022 i have extracted the Open Data of Switch DNS Zone Data for the .ch Zone and wrote a Blog Article how i imported it into a SQL Database.
I’ve written a PowerShell Script “Get-Mailprotection” and published it on GitHub and on the PowerShell Gallery.
The Script will extracts Information for a Domain like:
- DNS Zone Signed (DNSSEC)
- CAA (Certification Authority Authorization)
- MX (MailExchanger)
- STARTTLS
- TLS Certifcate Issuer
- SMTP Banner
- SPF (Sender Policy Framework)
- DKIM (DomainKeys Identified Mail)
- DMARC (Domain-based Message Authentication, Reporting and Conformance)
- DANE (DNS-based Authentication of Named Entities)
- BIMI (Brand Indicators for Message Identification)
- MTA-STS (SMTP MTA Strict Transport Security)
- MTA-STS Web (https://mta-sts.domain.tld/.well-known/mta-sts.txt)
- TLS-RPT (TLS Reporting)
- Autodiscover
- Lyncdiscover
- Skype4B / Teams Federation
- M365 Tenant
- SecurityTXT
Instead of only the sample of 100'000 Domains from 2015 i have then scanned all the 2.4 Mio .ch Domains. That took me about 2 Months (September/October 2022).
I’ve created the Swiss Domain Security Report Q3 2022
2023
This year i’ve changed some things:
I’ve added some new Properties to Get-Mailprotection, fixed several Bugs, created a better return Object and added a -silent Parameter.
- SecurityTXT
- SMTPBanner
- SMTP Certificate Issuer
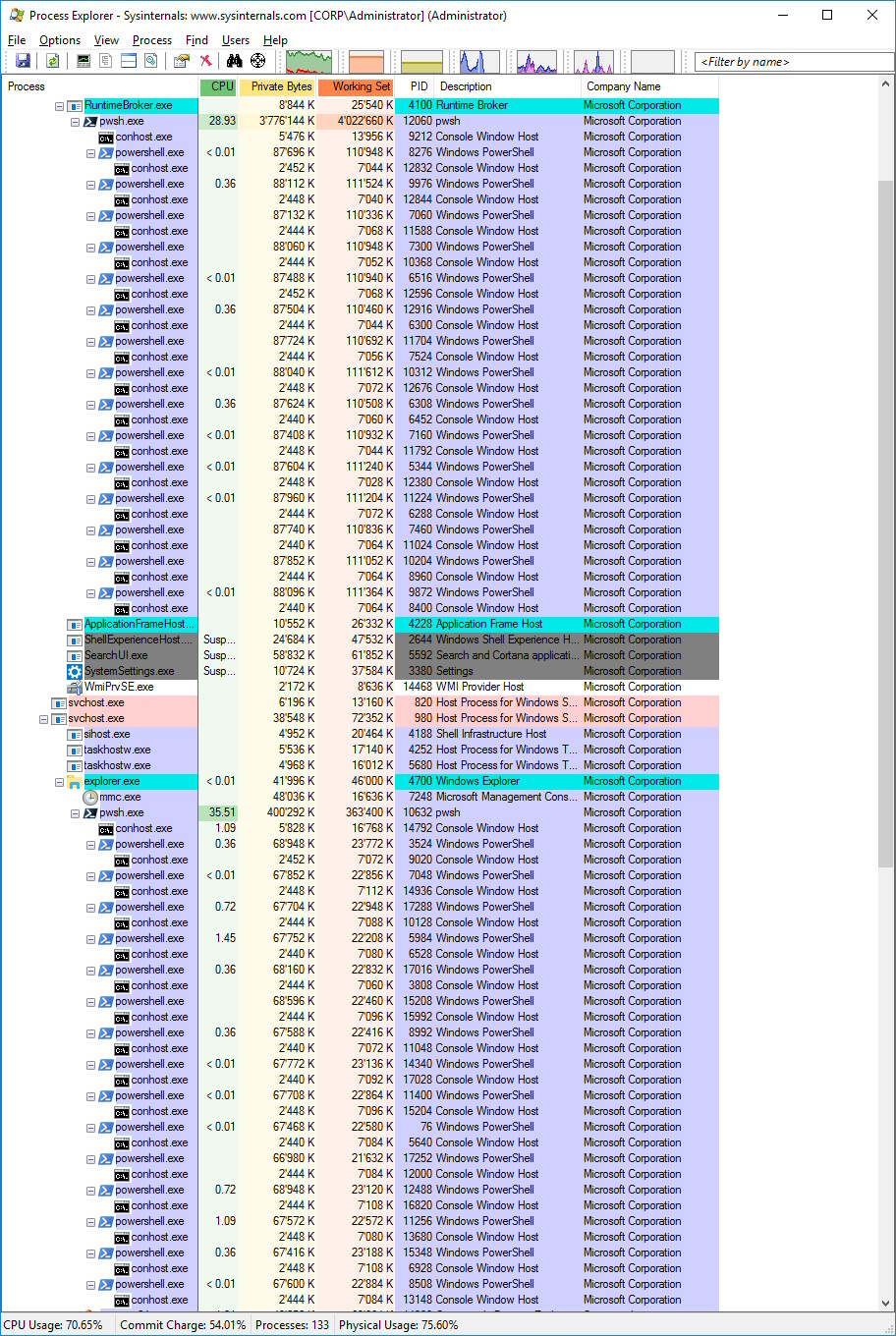
I used the Get-Mailprotection Script to Analyze all the .ch Domains. Turns out it was way more stable than last year. But still took about 8 Weeks to analyze (4vCPU’s / 16 GB RAM)
I used PowerShell 7 and run a Scriptblock with the -paralell Parameter. It’s interesting to see, that the Childprocesses are PowerShell 5.1.
I have used two PowerShell Scripts running each with 10-15 Childprocesses
- from A –> Z
- from Z –> A
Timeline
- September 2023: Getting .ch Zone Data and import into SQL DB
- Oktober / November 2023: Running the Script and gathering Data
- January 2024: Analysis and Report
Overview
My main Focus on this Project was related to Domain and Mailsecurity - but there are other aspects i did NOT consider like:
- HTTP/HTTPS of Website
- HTTPS TLS Version used
- HTTP Strict Transport Security Cheat Sheet (HSTS)
- HTTP Security Header
.ch Domains
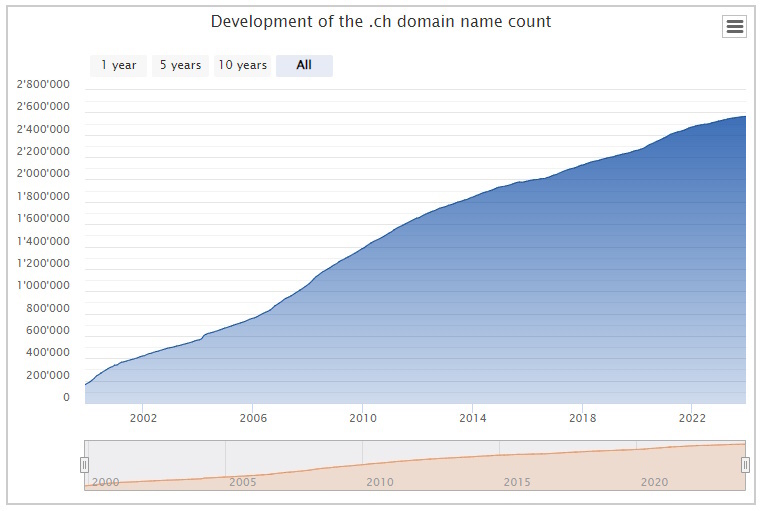
- 2'516'443 .ch Domains (September 2023) https://www.nic.ch/statistics/domains/
- 122'446 Domains more than about a year ago
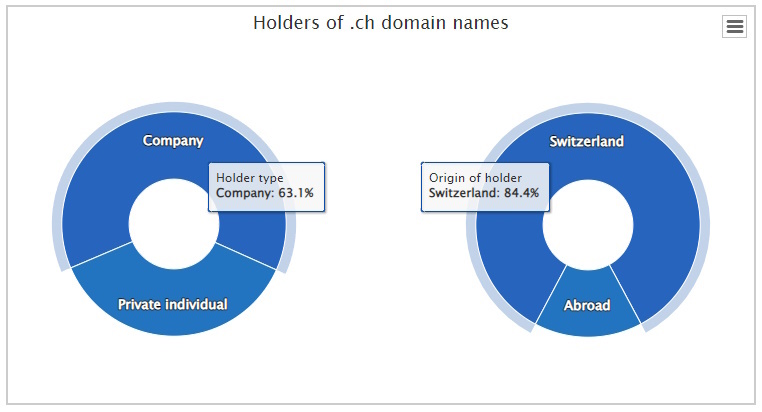
.ch Domain Holders (Company / private Individual) https://www.nic.ch/statistics/holders/
- 63.1% (about 1'587'875) of the Domains are owned by a Company
- 36.9% (about 928'567) of the Domains are owned by a private Individual
- 84.4% of the Domain Holders are located in Switzerland https://www.nic.ch/statistics/countries/
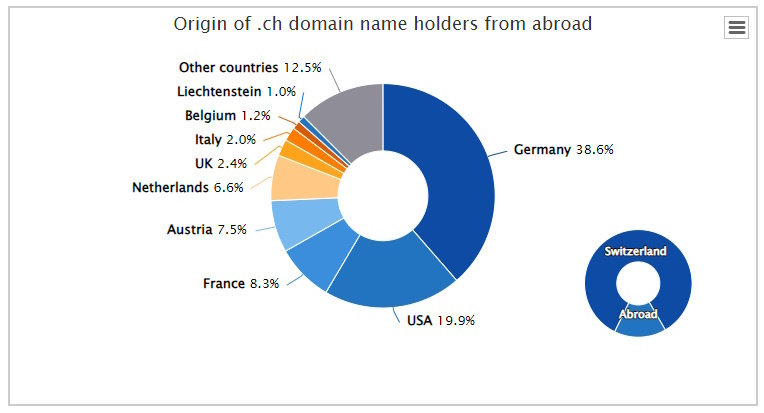
Top .ch Domain Holders outside Switzerland
- 38.6% Germany
- 19.9% USA
- 8.3% France
- 7.5 % Austria
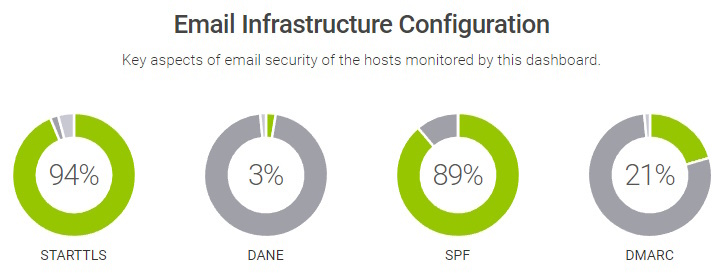
Hardenize
An overview about Security the top 1'000 .ch Domains is maintained by Switch
These are probably big companies with professional IT and Security Teams. So these Results do not represent the whole Market.
Domains
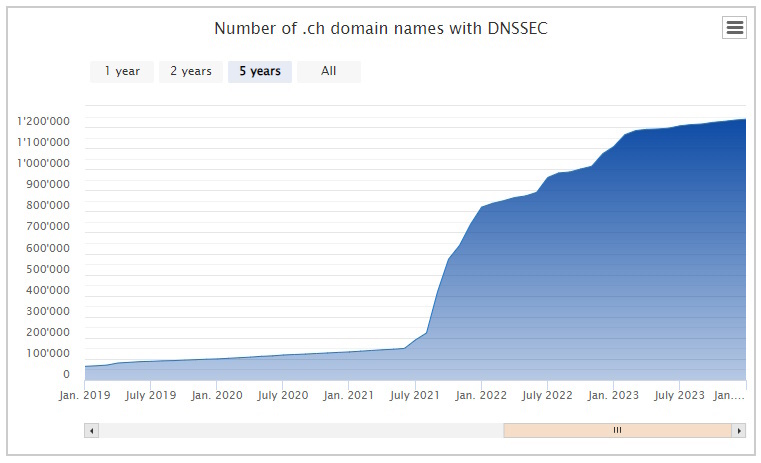
- 48.34% (1'216'341) of the DNS Zone Signed (DNSSEC) https://www.nic.ch/statistics/dnssec/
- with a huge bump since summer 2021
- 236'376 DNSSEC Domains more than about a year ago
- 13.75% (346'097) of the NS Records point to Hostpoint
- 5.51% (138.607) of the NS Records point to Infomaniak
- 3.23% (81'347) of the NS Records point to Cyon
- 2.94% (73'901) of the NS Records point to Hoststar
- 1.39% 35'095) of the NS Records point to Jimdo
- 0.23% (5'781) of the NS Records point to Azure DNS
- 2.66% (67'006) are internationalized domain name (IDN) using Punycode
CAA (Certification Authority Authorization)
- CAA exists since 2019 rfc8659
- 1.36% (34'299) of all .ch Domains support CAA
- 6'278 Domains more than about a year ago
SecurityTXT
I have checked for Security.txt on https://domain.tld/security.txt (old) and https://domain.tld/.well-known/security.txt (new)
- Exists since April 2022 rfc9116 More Info: https://securitytxt.org/
- 4.73% (119082) of all .ch Domains that has a SecurityTXT
Summary Domains
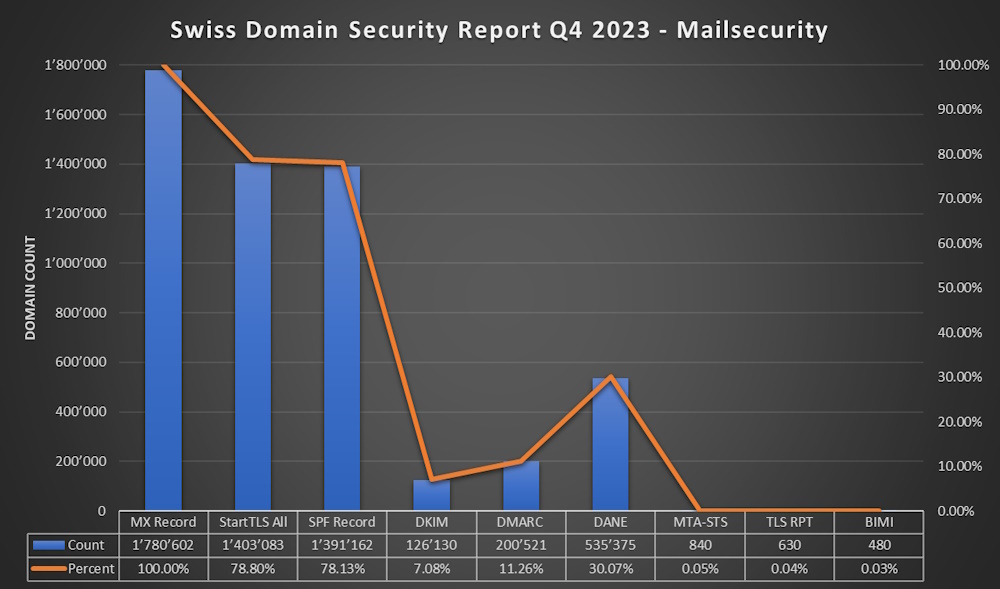
Mailsecurity
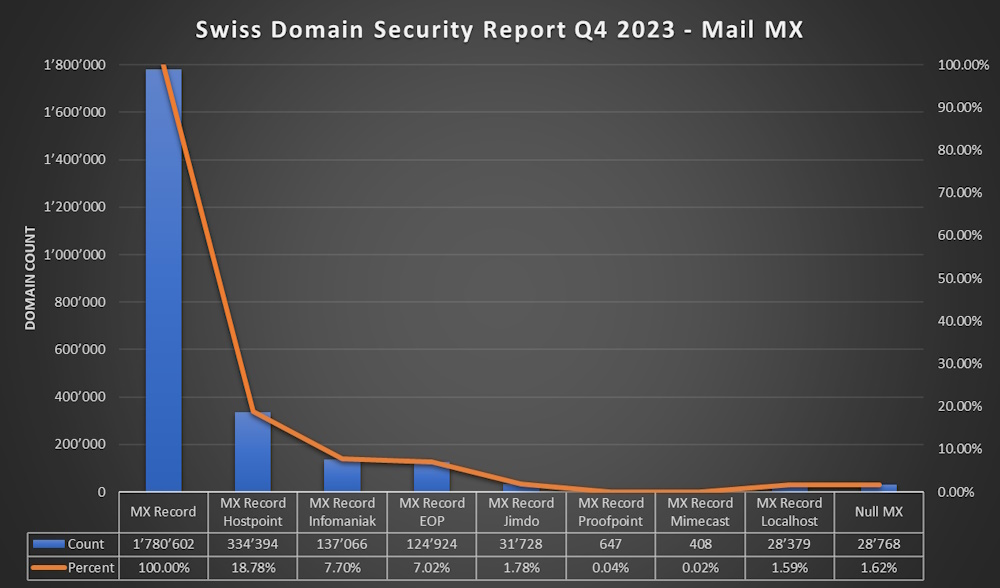
MX (Mail Exchange)
- MX Record exists since 1987 defined here rfc1035
- 70.76% (1'780'602) of all Domains have a MX Record
- 18.78% (334'394) of Domains with MX point to Hostpoint
- 7.70% (137'066) of Domains with MX point to Infomaniak
- 7.02% (124'924) of Domains with MX point to Exchange Online
- 1.78% (31'728) of Domains with MX point to Jimdo
- 0.04% (647) of Domains with MX point to Proofpoint
- 0.02% (408) of Domains with MX point to Mimecast
- 1.62% (28'768) of Domains use “Null MX” rfc7505 (sadly not supportet by Exchange Server or Exchange Online)
- 1.59% (28'379) of Domains with MX point localhost 😂 - (Mostly parked Domains)
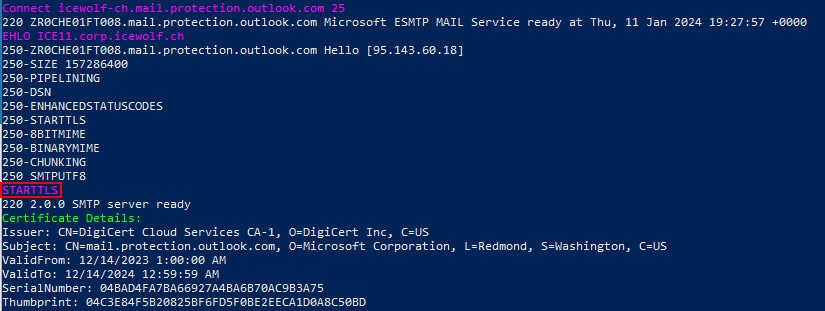
StartTLS
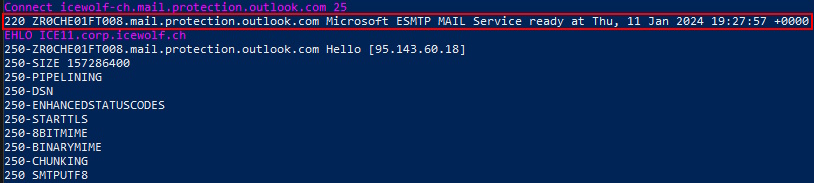
I’ve connected to every MX Record on Port 25 and checked for a “STARTTLS” Response to a EHLO command
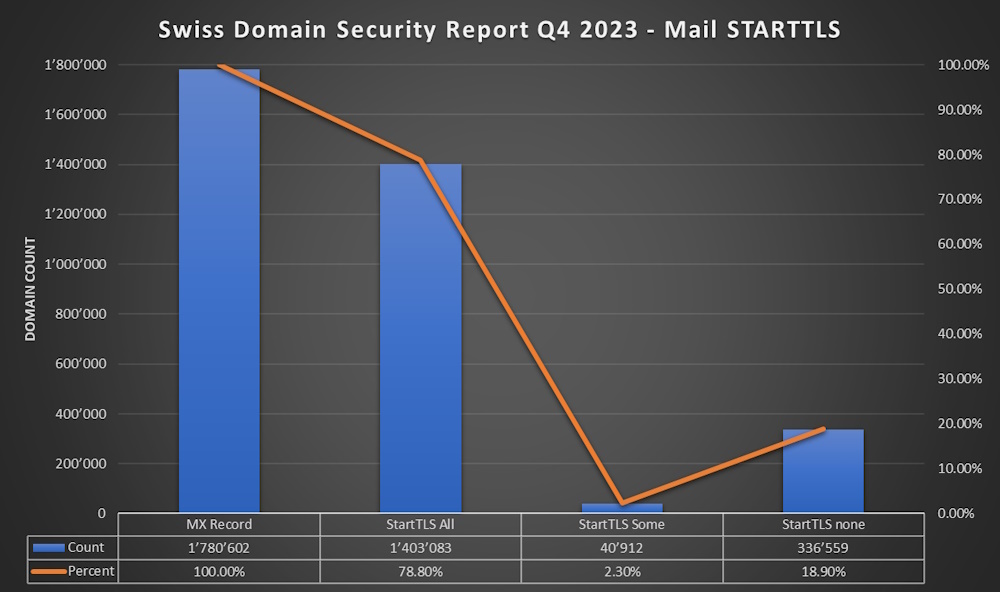
The Results of STARTTLS
- 78.80% (1'403'083) of all Domains with MX supports STARTTLS (on all MX records)
- 2.30% (40'912) of all Domains with MX supports STARTTLS (on some MX records)
- 18.90% (366'559) of the Domains with MX do not support STARTTLS
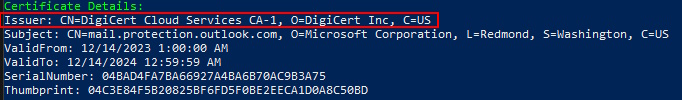
SMTP Certificate Issuer
When STARTTLS was available i’ve checked the Certificate Details and stored the Certificate Issuer (Certificate Authority that issued the Certificate)
Results of SMTP Certificate Issuer (CA)
The Report is based on the O=(Organization) Attribute of the CA Certificate
- 30.08% (695'778) O=Sectigo Limited
- 13.22% (235'465) O=Lets Encrypt
- 12.62% (224'646) O=DigiCert Inc
- 4.38% (78'033) O=GlobalSign nv-sa
- 2.78% (51'182) O=Google Trust Services LLC
- 1.70% (30'255) O=Deutsche Telekom Security GmbH
- 0.93% (16'477) O=“GoDaddy.com, Inc.”
- 0.22% (3'866) O=SwissSign AG
- 0.15% (2'719) O=“Entrust, Inc.”
Some Certificate Authorities have diffrent Brands. For Example:
- Digicert: Digicert, Geotrust, RapidSSL, Thawte\
- GlobalSign: AlphaSSL
It’s quite Impressive that Let’s Encrypt CA is used for more than 13% on SMTP. I have to admit, i was not aware of Sectigo CA before this Report.
I’ve written an Article how to Automate Exchange Certificate renewal with Let’s Encrypt
SMTP Banner
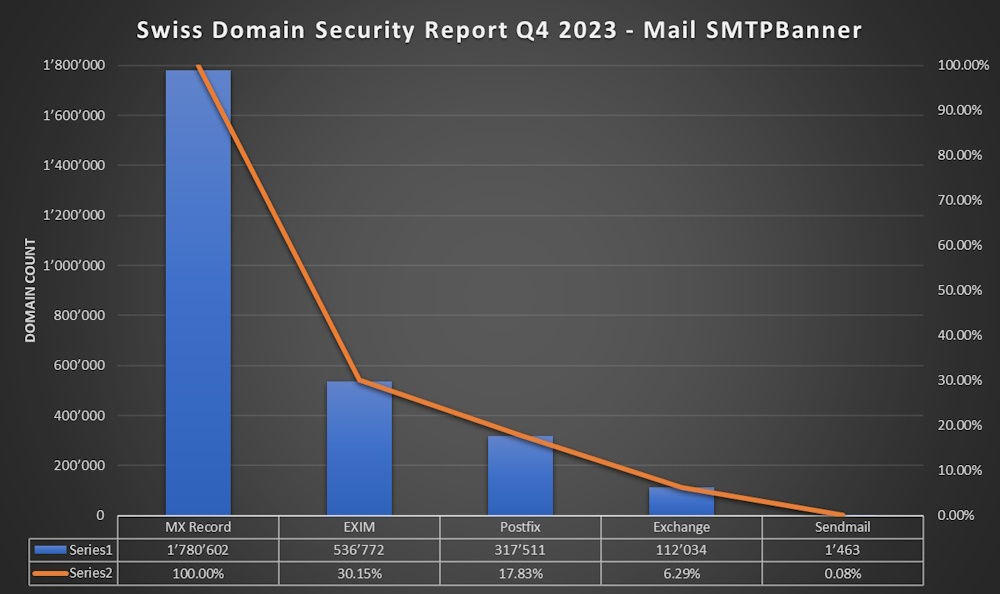
It’s clear that not all Mailservers will show the Software or even Version in the SMTP Banner. But a lot of Mailserver still do that and it’s interesting to see what are the most used Mailservers.
SMTPBanner Results
- 30.15% (536’772) EXIM
- 17.83% (317’511) Postfix
- 6.29% (112’034) Exchange/Exchange Online
- 0.08% (1’463) Sendmail
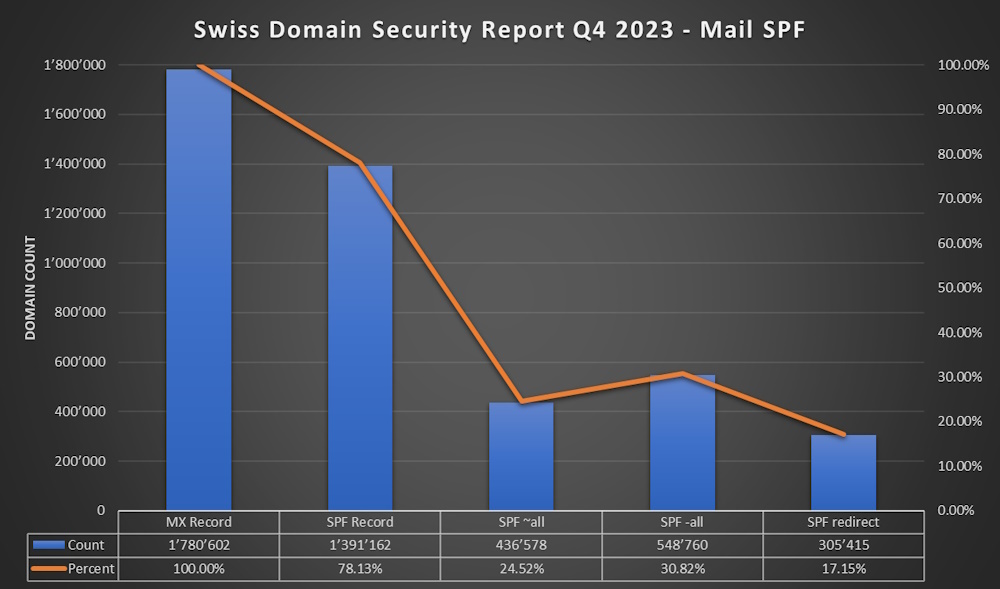
SPF (Sender Policy Framework)
- SPF exists since 2003 with Updates 2006 and 2014 rfc7208
- 78.13% (1'391'162) of Domains with MX have a SPF Record
- 24.52% (436'578) of Domains with MX have “SPF -all”
- 30.82% (548'760) of Domains with MX have “SPF ~all”
- 17.15% (305'415) of Domains with MX have a SPF Redirect
- 2.99% (53'180) of Domains with MX have (v=spf1 -all)
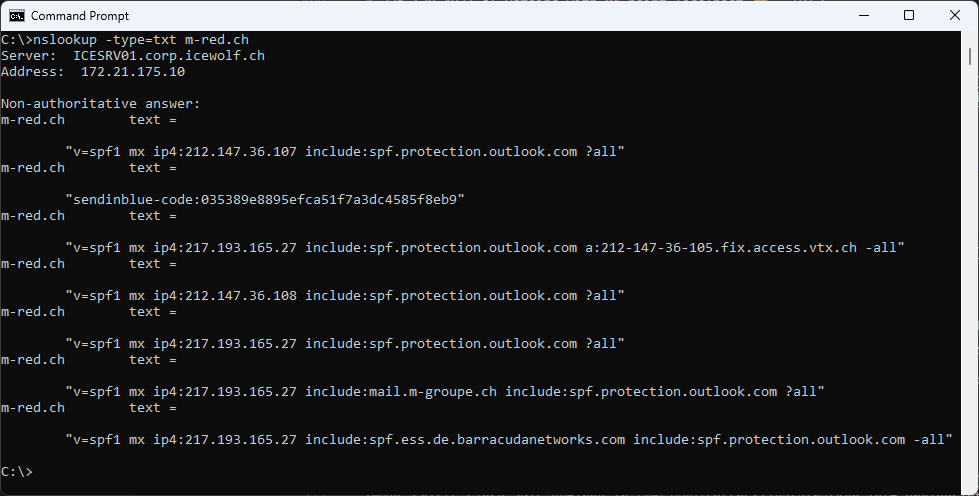
- 0.36% (6'441) of Domains with MX have Multiple SPF Records
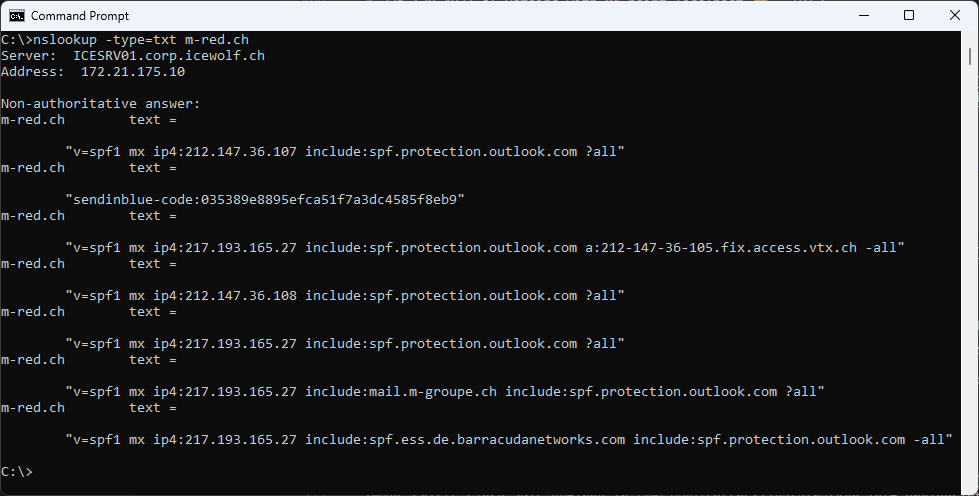
Bad Example: nslookup -type=txt m-red.ch (does not work like that)
DKIM (DomainKeys Identified Mail)
It is defined in rfc6376 from 2011 with updates in rfc8301 in 2018 and rfc8463 in 2018.
Note: due the fact that the Selector can be anything it’s hard to determine DKIM Records. I’ve tried to figure out if the _domainkey.domain.tld Zone exists. But depending on the DNS Server configuration the Results vary and there is almost no way to figure it out - except of receiving a Mail from that domain.
- 7.08% (126’130) of Domains with MX have a high chance of having a DKIM Record
- 64.54% (1’149’289) of Domains with MX might have a DKIM Record or not
As you can see the spreading of the Results is so big - it’s unknown how many Domains really use DKIM. You can look at the DMARC Numbers - because DMARC is based on SPF and DKIM.
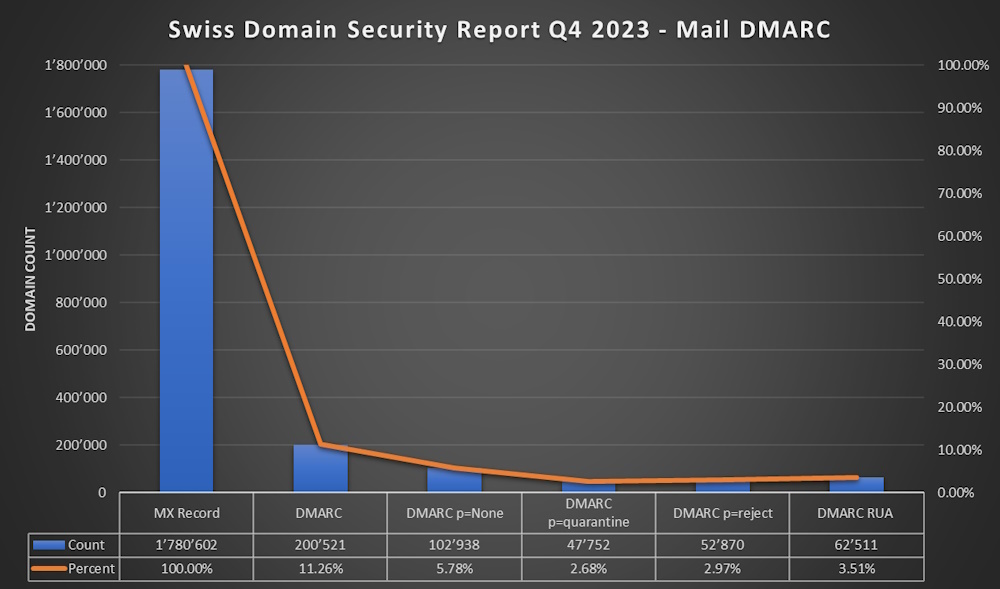
DMARC (Domain-based Message Authentication, Reporting and Conformance)
- DMARC Exists since 2015 defined in rfc7489
- 11.26% (200'521) of Domains with MX have a DMARC Record
- 5.78% (102'938) p=none
- 2.68% (47'752) p=quarantine
- 2.97% (52'870) p=reject
- 3.51% (62'511) have a rua defined
DANE (DNS-based Authentication of Named Entities)
- Exists since 2015 rfc7673
- Requires DNSSEC
- I’ve explained how DANE works in one of my Blog Articles
- 30.06% (535'208) of the Domains with MX have a DANE Record
- 27.66% (492'471) use “3 1 1” (Hash of Servercertificate without Certificate Chain / Hash of Public Key and algorithm / SHA-256 hash)
MTA-STS (SMTP MTA Strict Transport Security)
- Exists since 2018 rfc8461
- 0.05% (840) of the Domains with MX support MTA-STS
TLSRPT (SMTP TLS Reporting)
- Exists since 2018 rfc8461
- 0.04% (630) of the Domains with MX support TLS-RPT
BIMI (Brand Indicators for Message Identification)
- Exists since 2021 but is still under development IETF BIMI Draft
- 0.02% (298) of all .ch Domains Support BIMI / only 14 with a Certificate
- Sadly not supported by Microsoft
More Resources:
You can try to Vote for one of these two Suggestions in the Microsoft Feedback Portal
M365 Tenant
- 5.76% (144'948) of all .ch Domains have a M365 Tenant
- 12.34% (17'882) of Domains with an M365 Tenant have DKIM enabled (way to low)
- 67% (97'400) of Domains with an M365 Point the MX to EOP (*protection.outlook.com)
- 110'657 unique Tenants with .ch Domains
Summary Mailsecurity
Let’s wrap it up
- It is amazing that DNSSEC has improved from 40.9% to 48.34% in just one year
- STARTTLS is about 80%. That’s impressive - the goal should be 100%
- SPF has improved to 78%. Sadly only 30% have “-all” what should be standard (in my opinion)
- DKIM is hard to detect via DNS. Should be Standard on every M365 Tenant - as Microsoft makes this very easy
- DMARC has improved from 7.8% to 11.26. Half of it with “p=none” - Still a long way to go and “p=reject” should be standard
- DANE has improved from 28.3% to 30.06% - surprising high due to the fact it’s quite complex to set up and it has a DNSSEC Requirement
- MTA-STS/TLS-RPT is surprising low at 0.05% as it’s less complex than DANE. I bet this will still increase over time.
- BIMI still very low and VMC Certificates have high costs and require registered Trademarks and Logos. It will stay like that until Microsoft is supporting BIMI
Call to Action
Let’s make Email better and implement those well known Techniques to improve the Domain and Mailsecurity in Switzerland.
That means you, as an Mailserver Administrator, you as a Provider, you as a CISO, you as a Business Representive… Take action and help to improve the Security in Switzerland..
I would like to hear about your actions on Twitter, LinkedIn or BlueSky with the Hashtag #SwissDomainSecurityReport 😍
Regards
Andres Bohren