KeePass 2.54 released

Hi All,
Lately KeePass was in the Press because of the Security Eploit below.
Simple Security Exploit Allows Retrieval Of KeePass Master Password, Patch Inbound
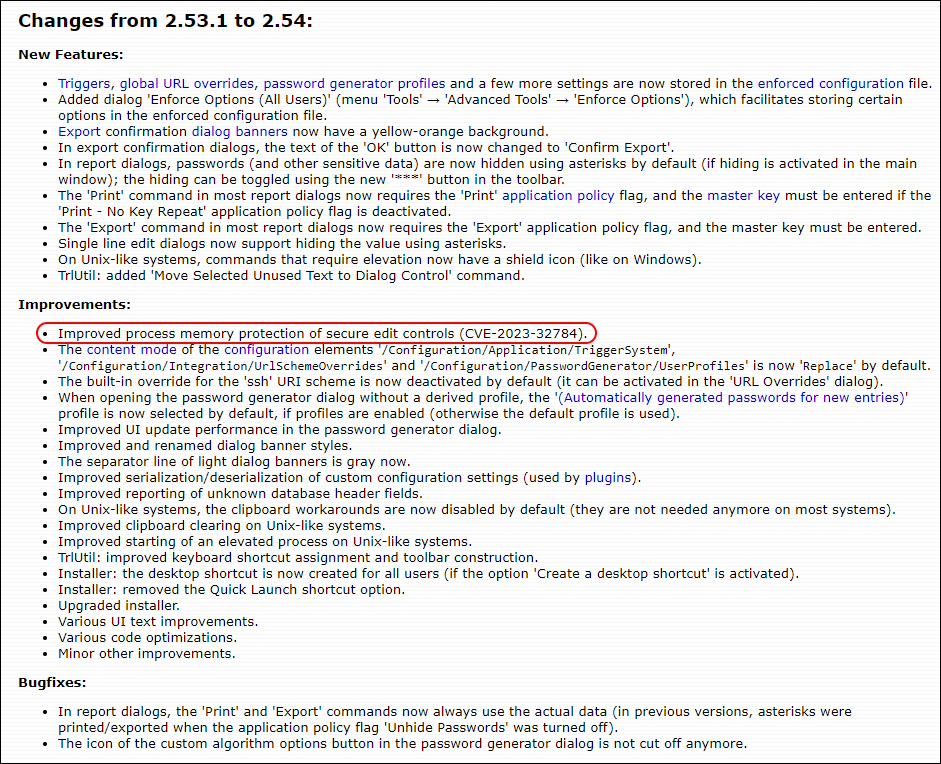
In short, KeePass 2.53 and earlier loads the master password into memory in plaintext when it is entered via the keyboard. This means all an attacker has to do is get their hands on a memory dump regardless of if that comes from “the process dump, swap file (pagefile.sys), hibernation file (hiberfil.sys), various crash dumps or RAM dump of the entire system.”
More Informations can be found here CVE-2023-32784
Now a Version has been released that fixes this Problem KeePass 2.54 released
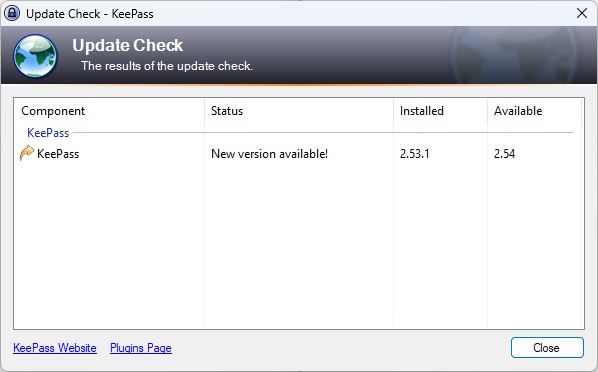
Today a saw this Update
Changes and reference to the CVE
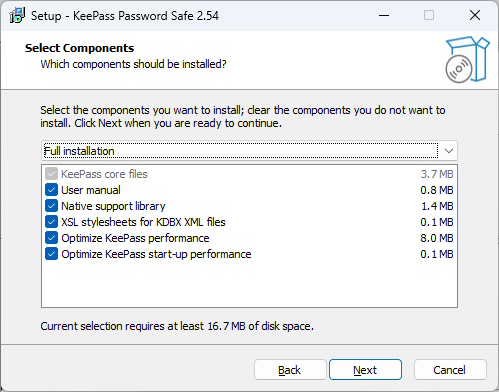
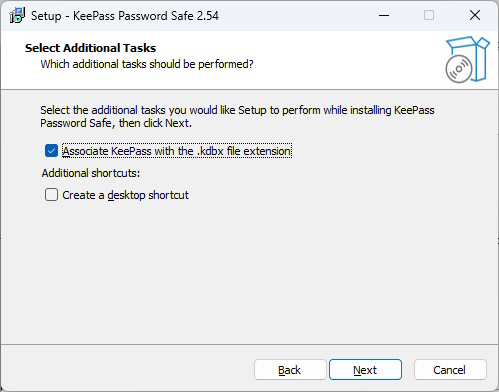
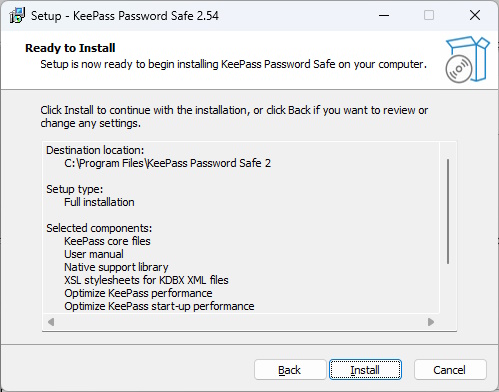
Update Process
Regards
Andres Bohren